Cyber threats are becoming more rampant, more sophisticated, and increasingly targeted at small and medium-sized businesses. Yet, many SMEs still believe cybersecurity frameworks like ISO 27001 are too complex, too expensive, or only relevant for large enterprises.
The reality is quite different.
The ISO/IEC 27001:2022 practical guide for SMEs was specifically designed to help smaller organizations implement a structured, scalable approach to information security without requiring massive resources or dedicated teams.
The guide is designed to simplify the complexities of implementing an Information Security Management System (ISMS) tailored to the unique needs and constraints of SMEs.
The ISO/IEC 27001 guide for SMEs aims to guide small and medium-sized enterprises (SMEs) on developing and implementing an information security management system (ISMS), based on the International Standard ISO/IEC 27001:2022, Information security, cybersecurity and privacy protection — Information security management systems — Requirements.
At its core, ISO 27001 is not about technology. It is about managing risk. It provides a framework for protecting the confidentiality, integrity, and availability of your data while building trust with customers, partners, and regulators.
In the rapidly evolving digital landscape, cybercrime continues to pose serious threats to businesses, especially to small and medium-sized enterprises (SMEs), which make up the majority of the global market. ISO/IEC 27001:2022 is a critical tool, providing SMEs with robust strategies to manage information security risks effectively.
Importantly, the standard is flexible. SMEs are not expected to start from scratch. Instead, they are encouraged to build on existing processes, adapt their current operations, and implement controls that fit their size, structure, and resources.
In this article, we break down what ISO 27001 means for Small and Medium-sized Enterprises, why it matters, and how your organization can take practical steps to build a strong, resilient security foundation.
SMEs are the backbone of the global economy
According to the World Economic Forum, Small and medium-sized enterprises (SMEs) are the backbone of the global economy. With around 400 million enterprises worldwide, SMEs account for approximately 90% of all firms globally, generate 70% of employment, and contribute up to 70% of global GDP.
SMEs account for the vast majority of businesses worldwide and often have specific needs.
Small and medium-sized enterprises (SMEs) often face unique challenges, such as restricted access to finance, cash flow and resource constraints, or a lack of understanding of cybersecurity risks that can lead to security compromises.
Small and Medium Enterprises (SMEs) are businesses classified by limited staff, revenue, or assets, typically having fewer than 250 employees in the EU or under 500 in Canada and the U.S.
What is ISO/IEC 27001?
ISO/IEC 27001 is the world’s leading standard for ISMSs, providing organizations with guidance on establishing, implementing, maintaining and continually improving an ISMS. It defines requirements for an ISMS and helps organizations secure their information assets by identifying and managing risks – a vital task in today’s digital world.
ISO/IEC 27001 is the premier international standard for information security management systems (ISMS), providing a risk-based framework to protect data confidentiality, integrity, and availability.
Implementing ISO/IEC 27001 means your organization or business has put in place a system to manage risks to the security of data owned or handled by the company, and that this system adheres to all the best practices and principles enshrined in the standard.
By using ISO/IEC 27001, you demonstrate to stakeholders and customers that you are committed to managing information securely and safely. It is a unique way to promote your organization, celebrate your achievements and prove that you can be trusted.
What is an ISMS (Information Security Management System)?
A management system is defined as a set of interrelated or interacting elements within an organization that establish policies and objectives, as well as processes to achieve them.
A management system is the way an enterprise directs and controls the business activities related (either directly or indirectly) to achieving its intended objectives and results.
For an ISMS, the objectives are the preservation of the confidentiality, integrity and availability of the information under its control. Your business activities should be directed, controlled and managed in a way that achieves these information security objectives.
ISO/IEC 27001 specifies the requirements for establishing, implementing, maintaining and continually improving an ISMS.
An Information Security Management System (ISMS) is a structured approach to managing sensitive information.
The implementation, use, and maintenance of an ISMS should be considered an investment that will deliver benefits and improvements to your information security.
It ensures that your organization protects:
- Confidentiality – Only authorized people access data
- Integrity – Data is accurate and not tampered with
- Availability – Systems and data are accessible when needed
ISO 27001 is NOT just for big enterprises
Why does having an Information Security Management System matter for SMEs?
1. Cyber threats are increasing
SMEs are prime targets due to weaker defenses.
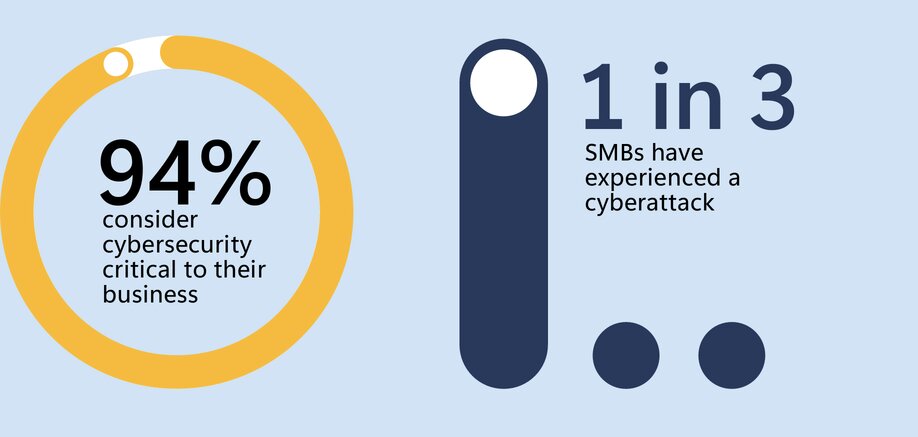
Ninety-four percent of SMBs consider cybersecurity critical, but without the tools and internal expertise to keep people, data, and devices secure, SMBs are vulnerable. – Microsoft Security Report

2. Customers demand trust
Clients increasingly expect vendors to demonstrate security maturity.
When it comes to the brands they buy, 88% say trust is as important as price and quality – Edelman Trust Barometer
3. Compliance is expanding
Privacy laws, contracts, and regulators require stronger data protection.
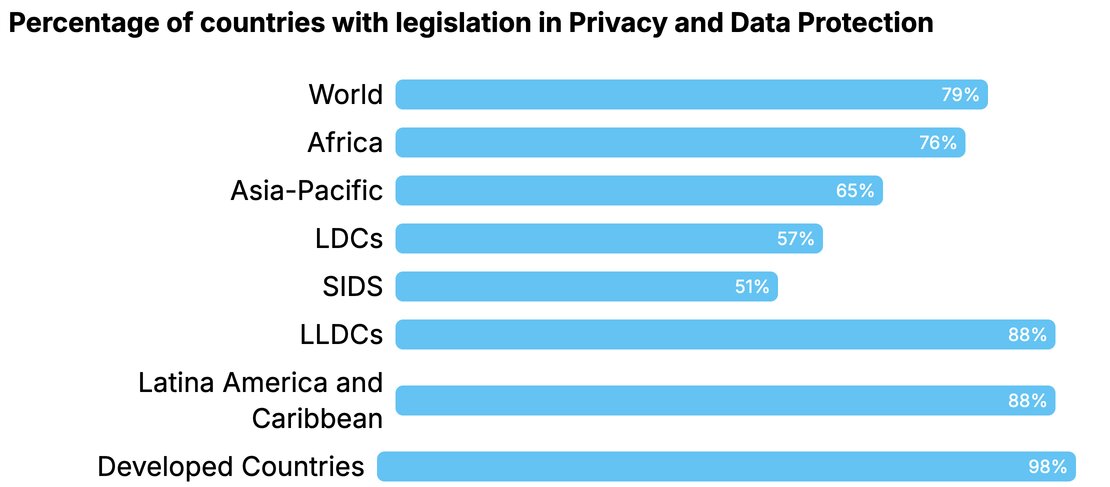
Over 70% of countries worldwide now have data protection and privacy legislation in place, reflecting the global expansion of regulatory requirements (UNCTAD)
4. It creates a competitive advantage
ISO 27001 can:
- Unlock enterprise deals
- Improve credibility
- Enable global market access
Organizations with mature security programs reduce breach costs by up to $1.76 million on average (IBM Security Cost of a Data Breach Report).
ISO/IEC 27001 is the world’s best-known standard for information security management systems (ISMS). It defines the requirements an ISMS must meet.
Step-by-Step: How SMEs Can Implement ISO 27001
Step 1: Understand Your Business Context
Define:
- What your business does
- What data do you handle
- What risks exist
Consider:
- Customers
- Regulations
- Technology
- Industry threats
Step 2: Identify Your Critical Information Assets
Examples:
- Customer data
- Financial records
- Intellectual property
- Cloud systems
Step 3: Conduct a Risk Assessment
Ask:
- What could go wrong?
- What is the impact?
- How likely is it?
Examples:
- Phishing attacks
- Cloud misconfigurations
- Insider threats
Step 4: Define Security Controls
Based on risks, implement controls such as:
- Identity and access management
- Multi-factor authentication
- Backup and recovery
- Logging and monitoring
- Security awareness training
Step 5: Establish Policies and Procedures
Document:
- Access control policies
- Incident response plans
- Data protection guidelines
Step 6: Assign Roles and Responsibilities
Even in small teams:
- Define ownership
- Ensure accountability
Step 7: Monitor and Improve
Track:
- Security incidents
- Security posture
- Control effectiveness
- Audit findings
Practical Roadmap for SMEs
Phase 1: Foundation (0–3 months)
- Understand ISO 27001 basics
- Identify assets and risks
- Define scope
Phase 2: Implementation (3–6 months)
- Deploy key controls
- Create policies
- Train staff
Phase 3: Maturity (6–12 months)
- Conduct internal audits
- Improve processes
- Prepare for certification (optional)
ISO 27001 Checklist for SMEs
Use this as a quick self-assessment:
Governance
Defined security objectives
Leadership involvement
Risk Management
Risk assessment completed
Risk treatment plan defined
People
Security awareness training in place
Roles and responsibilities assigned
Technology
MFA enabled
Logging and monitoring implemented
Backup systems in place
Processes
Incident response plan
Access control policy
Data protection guidelines
ISO 27001 doesn’t have to be complex—but it does need to be done right.
At Reputiva, we help small and growing businesses design and implement practical, scalable security programs aligned with ISO 27001 without unnecessary complexity or overhead.
Start with a Security & Compliance Assessment to understand your current gaps and build a clear roadmap toward ISO 27001 readiness.


