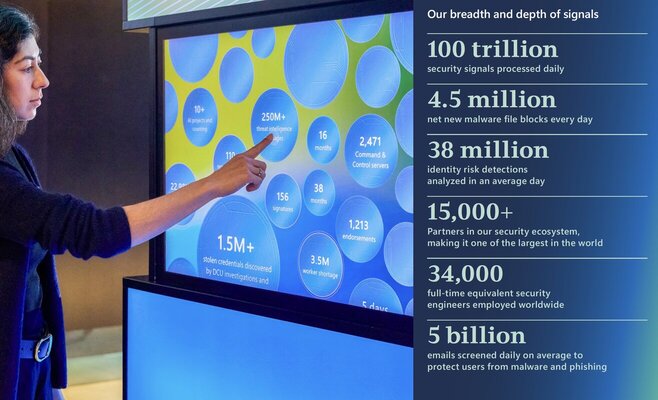
The 2025 Microsoft Digital Defense Report (MDDR) showcases the scale and sophistication of today’s cyber threats, the impact of emerging technologies on those threats, and the strategies that leaders, governments, and defenders can use to defend against them. Microsoft provides a comprehensive view into today’s evolving cyber threat landscape, powered by trillions of signals across identities, endpoints, cloud platforms, and global infrastructure.
According to the 2025 MDDR, cyber threats are becoming more sophisticated, more automated, and increasingly driven by nation-state actors and AI-enabled techniques. From identity-based attacks to cloud misconfigurations and supply chain risks, the attack surface continues to expand faster than most organizations can secure it.
As organizations accelerate their adoption of cloud, SaaS, and AI-driven technologies, the attack surface is expanding faster than traditional security models can keep up.
In this article, we break down the key threats highlighted in the MDDR report and what it means for your cloud security, identity strategy, and overall risk posture.
Report year: Microsoft fiscal year 2025 (July 1, 2024-June 30, 2025) unless otherwise stated.
Artificial Intelligence in cybersecurity is already creating new challenges for security organizations as they rush to adapt systems, understand new threats, and equip their people with new knowledge to keep pace.
For security leaders, the imperative is clear: cybersecurity must be a priority, embedded into the fabric of organizational strategy and addressed regularly as part of risk management.
Traditional perimeter defenses are no longer sufficient. Resilience must be designed into systems, supply chains, processes, and governance. New types of threats will emerge with increasing frequency; being informed and prepared is critical.
2025 Microsoft Digital Defense Report Report Update
AI as both a defensive necessity and a target
We’re witnessing adversaries deploy generative AI for a variety of activities, including scaling social engineering, automating lateral movement, engaging in vulnerability discovery, and even real-time evasion of security controls. Autonomous malware and AI-powered agents are now capable of adapting their tactics on the fly, challenging defenders to move beyond static detection and embrace behavior-based, anticipatory defense.
At the same time, AI systems themselves have become high-value targets, with adversaries amping up use of methods like prompt injection and data poisoning to attack both models and systems, which could lead to unauthorized actions, data leaks, theft, or reputational damage.
Diverse vectors for initial access
In today’s world, campaigns rely on multi-stage attack chains that mix tactics and techniques such as social engineering and technical exploits.
The pervasive threat of infostealers
Increasingly, adversaries aren’t breaking in, they’re logging in. In today’s specialized cybercrime economy, access is essential, and infostealers are a way for operators to collect credentials and tokens for sale on the dark web. Follow-on activities by the buyers of compromised credentials can include ransomware, data exfiltration, and/or extortion.
Nation-state actors expanding operations
Geopolitical objectives continue to drive a surge in state-sponsored cyber activity, with a notable expansion in targeting the communications, research, and academia sectors. Nation-states continue to accelerate AI use to evolve their cyber and influence operations, making them more scalable, advanced, and targeted.
Microsoft Security Depth
Key Takeaways
1. Phishing-resistant MFA is the gold standard for security
No matter how much the cyber threat landscape changes, multifactor authentication (MFA) still blocks over 99% of unauthorized access attempts, making it the single most important security measure an organization can implement. Phishing-resistance provides an even more secure solution.
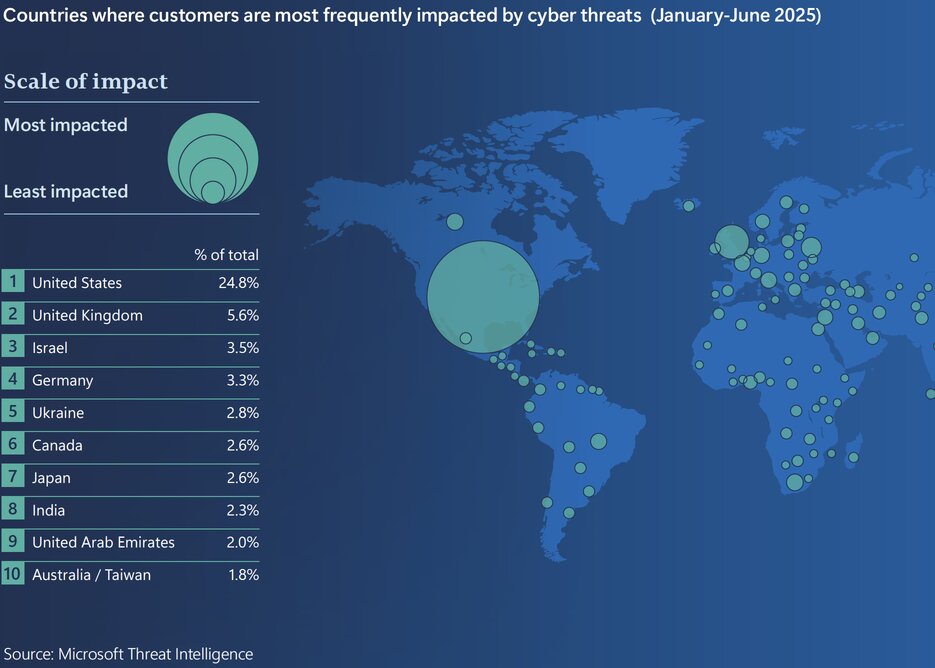
2. Adversaries are targeting identities that enable access to data
Government organizations, information technology (IT) companies, and research and academic institutions were the most impacted by cyber threats this year. Among other data they hold that might interest adversaries, these organizations store vast amounts of personally identifiable information (PII), whose theft enables future attacks. Accessing organizational data has become a primary objective for threat actors. Government, NGO, and academic entities using legacy systems or operating with small IT teams and limited incident response capabilities should prioritize securing data and identity-facing assets.
3. Adversaries are using diverse—but well-known—initial access routes
Incident response investigations found that 28% of breaches were initiated through phishing or social engineering, 18% were via unpatched web assets, and 12% leveraged exposed remote services. Not only are adversaries heavily leveraging the ClickFix social engineering method to deliver malware this year, but threat actors are incorporating exploits for known vulnerabilities faster than ever.
4. Most attacks are for money, not espionage
More than half of cyberattacks with known motives had financial objectives such as extortion or ransom, while only 4% were motivated solely by espionage.
A security researcher may earn $10,000 for responsibly disclosing a vulnerability to a bug bounty program, but may earn over $100,000 by selling the same exploit to a cyber mercenary
5. Data exfiltration is the norm
Regardless of adversary motivations, accessing organizational data is now a primary goal for attacks. In the past year, Microsoft observed data collection in 80% of reactive engagements.
6. Workload identities are under threat
As organizations implement phishing-resistant MFA and conditional access policies, adversaries are pivoting to targeting identities and elevated privileges granted to service-to-service workloads like apps, services, and scripts that access cloud resources because service-based workloads are often implemented with elevated privileges but weak security controls.
7. Adversaries are conducting destructive attacks in the cloud
Microsoft saw an increase in campaigns aimed at disrupting Azure cloud customer environments through destructive actions such as ransomware or mass deletion. Additionally, over 40% of ransomware attacks now involve hybrid components.
8. Adversaries are already using AI as a multiplier
Adversaries have begun implementing AI across a range of malicious activities, including for automated vulnerability discovery or phishing campaigns, malware or deepfake generation, data analysis, and to craft highly convincing fraudulent messages.
9. Using AI can be both a benefit and a vulnerability
AI is driving rapid, substantial change. While it offers many benefits for organizations, particularly in cyber defense, AI can be attacked as well. As organizations implement the strengths of AI, they should also manage the weaknesses and potential exposure of sensitive data by protecting against threats like prompt injection, malicious tool invocation, and training data poisoning.
10. Quantum computing could challenge cybersecurity
Quantum computing has vast economic potential, but if used by malicious actors, it could threaten the encryption of sensitive data.

A significant portion of attacks begin by targeting an organization’s exposure footprint: perimeter web-facing assets (18%) and external remote services (12%) as well as—to a lesser degree— supply chains (3%).
What these trends mean for defenders:
Trust is not enough.
Familiar platforms and tools could be—and are—abused. It’s crucial to apply zero trust principles in your security model.
Endpoint visibility is insufficient.
Critical attack activity might occur outside the reach of endpoint detection and response (EDR).
Early-stage threats are critical signals.
Infostealers and credential theft should trigger investigation, not be dismissed as routine.
Emerging Threat Vectors
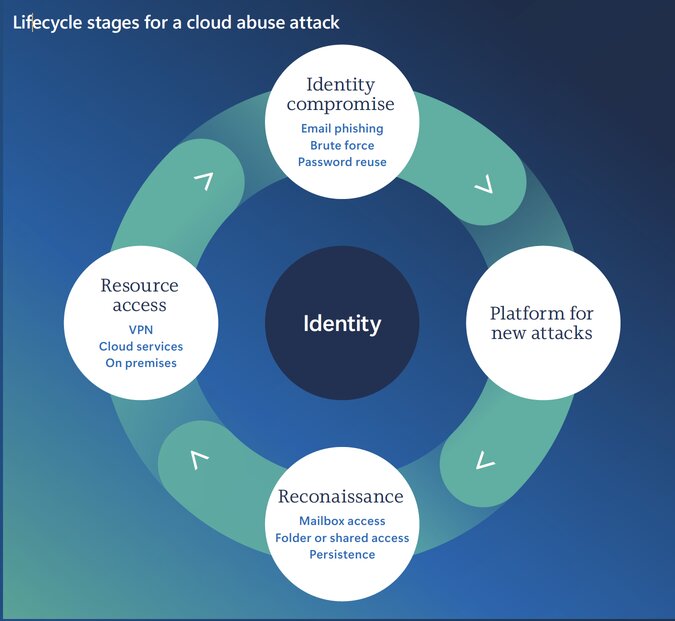
Identity, access, and the cybercrime economy
Modern multifactor authentication still reduces the risk of identity compromise by more than 99%.
From end users to workloads: The new horizon in identity threats
In the first half of 2025, identity-based attacks rose by 32%. This escalation may reflect adversaries’ increasing use of AI to craft highly convincing social engineering lures—posing new challenges for detection and response at scale.
Strategic threats to the research and academia sector
In 2025, it ranked among the top targets for threat actors due to its high-value IP, decentralized infrastructure, and expansive digital footprint. These conditions make it an ideal environment for adversaries to test and refine advanced attack techniques before deploying them against hardened targets such as government agencies and critical infrastructure.
In the first half of 2025, identity-based attacks surged by 32%, with research and academia accounting for 39% of all identity compromise incidents observed by Microsoft.
Synthetic Identities
Synthetic identities are also a rising risk. In the digital services realm, verifying user identity is a cornerstone of security. Deepfakes and AI-generated documents threaten to weaken those verification checkpoints.
AI-generated IDs are now often more convincing than real forgeries, growing by 195% globally in usage.
Top 10 recommendations
1. Manage cyber risk at the boardroom level
Treat cybersecurity as a business risk on par with financial or legal challenges. It is important that corporate boards and CEOs understand the security weaknesses of their organization. Track and report metrics like multifactor authentication (MFA) coverage, patch latency, incident counts, and incident response time to develop a comprehensive understanding of both your organization’s potential vulnerabilities and its preparedness in the event of a cybersecurity incident.
2. Prioritize protecting identities
Since identity is the top attack vector, enforce phishing-resistant multifactor authentication across all accounts, including administrative accounts.
3. Invest in people, not just tools
Cybersecurity is a whole-of-organization effort. Find ways to upskill your workforce and consider making security part of performance reviews. Culture and readiness—not just technology—are primary factors in both an organization’s defenses and its resilience.
4. Defend your perimeter
A third of attackers use crude tactics as the easy path into an organization’s exposed footprint, often looking beyond what you deploy to the vendors and supply chain you trust, including perimeter web-facing assets (18%), external remote services (12%), and supply chains (3%). Knowing the full scope of your perimeter, auditing the accesses you grant to trusted partners, and patching any exposed attack surface forces attackers to work harder to be successful.
5. Know your weaknesses and pre-plan for breach
Combine knowledge of the organization’s exposure footprint with organizational risk awareness to develop a proactive plan for responding to future breach. Tie security controls to business risks in terms the board can understand. Since a breach is a matter of when, not if, develop, test, and practice your incident response (IR) plan—including specific scenarios for ransomware attacks, which remain one of the most disruptive and costly threats to operations. How fast can you isolate a system or revoke credentials?
6. Map and monitor cloud assets
Since the cloud is now a primary target for adversaries, conduct an inventory on every cloud workload, application programming interface (API), and identity within the organization, and monitor for rogue virtual machines, misconfigurations, and unauthorized access. At the same time, work proactively to enforce app governance, conditional access policies, and continuous token monitoring.
7. Build and train for resiliency
If breaches are all but inevitable, resilience and recovery become key. Backups must be tested, isolated, and restorable, and organizations should have clean rebuild procedures for identity systems and cloud environments.
8. Participate in intelligence sharing
Cyber defense is a team, not individual, sport. By sharing and receiving real-time threat data with peers, industry groups, and government, we can make it harder for cyber adversaries to achieve their goals.
9. Prepare for regulatory changes
It’s more important than ever for organizations to align with emerging laws like the European Union (EU) Cyber Resilience Act or United States (US) critical infrastructure mandates, which may require reporting cyber incidents within a certain timeframe or Secure by Design practices. These regulations reinforce the importance of timely incident reporting and stronger internal oversight of an organization’s cybersecurity practices.
10. Start AI and quantum risk planning now
Stay ahead of emerging technologies. Understand both the benefits and risks of AI use within an organization and adjust your risk planning, attack surface exposure, and threat models appropriately. Prepare for a post-quantum cryptography (PQC) world by taking the time to inventory where encryption is used and create a plan to upgrade to modern standards as they evolve.
The insights from Microsoft’s report highlight a simple reality: traditional security approaches are no longer enough.
Reputiva works with organizations to implement Zero Trust architectures, strengthen identity security, and secure multi-cloud environments across AWS, Azure, and GCP.
Book a consultation to align your security strategy with today’s threat landscape.