Cloud Adoption is transforming how organizations build and scale their workloads, but it has also changed how security is implemented. We are moving from a centralized, perimeter-based model to a distributed, dynamic environment where misconfigurations, identity gaps, and limited visibility significantly increase risk. Cloud Security Posture Management (CSPM) tools have emerged to address this challenge.
According to the IBM Cost of a Data Breach Report 2025, cloud environments have become a primary target for attackers, with misconfiguration emerging as a key contributor to modern breaches. This aligns with findings from the 2025 Cloud Security Alliance Top Threats to Cloud Computing report, which ranks misconfiguration and inadequate change control as the number one cloud security risk, based on input from over 500 industry experts.
The above findings point to changing realities: cloud misconfiguration, operational complexity, and a lack of visibility are the leading factors driving cloud security risk. In cloud environments, traditional security approaches are no longer sufficient, hence the need for automated visibility and control for proactive risk management. This is where Cloud Security Posture Management (CSPM) becomes essential.
History of CSPM
Cloud Security Posture Management (CSPM) emerged as organizations struggled with misconfigurations and a lack of visibility in cloud environments. Early security approaches relied on manual processes and fragmented tools until Gartner formalized CSPM as a category around 2017-2018, focused on continuous monitoring, misconfiguration detection, and compliance enforcement.
As cloud adoption scaled, CSPM became a baseline capability for managing risk across multi-cloud environments and supporting compliance. It has since evolved into broader platforms like Cloud-Native Application Protection Platform (CNAPP), but it remains the foundation for addressing the most persistent cloud risk: misconfiguration.
What is Cloud Security Posture Management?
According to Microsoft, Cloud Security Posture Management (CSPM) is an automated security capability that continuously monitors cloud environments to identify misconfigurations, security risks, and compliance gaps. It provides centralized visibility across multi-cloud infrastructures (AWS, Azure, and GCP), helping organizations reduce the risk of data exposure and unauthorized access.
Core Functions of CSPM
- Continuous monitoring of cloud environments
- Misconfiguration detection and configuration management
- Visibility into cloud assets and risks
- Compliance monitoring and regulatory alignment
- Identity and access management (IAM) analysis
- Vulnerability scanning and risk detection
- Threat detection and incident response support
- Automated remediation and policy enforcement
- Protection against common cloud threats
- Integration with cloud platforms and security tools
Why CSPM Matters
Misconfigurations Are the #1 Cloud Risk
According to the Cloud Security Alliance Top Threats to Cloud Computing report, misconfiguration and inadequate change control are ranked as the top cloud security risks, based on input from over 500 industry experts.
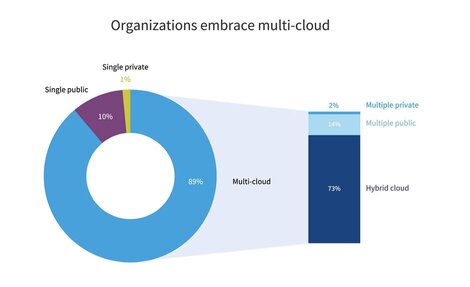
Cloud Complexity Is Increasing
Cloud environments are becoming more complex as organizations adopt multi-cloud strategies, SaaS platforms, and AI-driven workloads. According to the Flexera 2026 State of the Cloud Report, “complexity is compounded by simultaneous migration and repatriation, SaaS proliferation and the rapid adoption of AI.”
Lack of Visibility is a growing challenge
The Cloud Security Alliance identifies limited cloud visibility and observability as a key cloud security threat, highlighting the difficulty organizations face in tracking assets and risks across distributed environments.
Human Risk drives risk
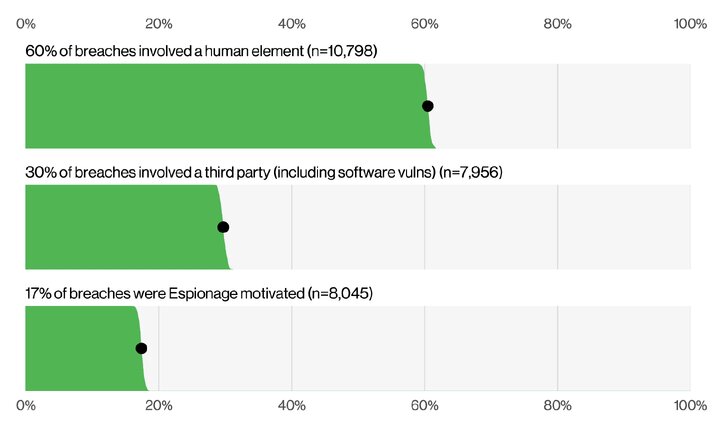
The human element remains a major driver of security risk. The Verizon 2025 Data Breach Investigations Report found that approximately 60% of breaches involve a human element, including errors, misconfigurations, and credential misuse.
CSPM in a Multi-Cloud World (AWS, Azure, GCP)
Each major cloud service provider offers native CSPM capabilities – AWS through Security Hub and Config, Azure through Defender for Cloud, and GCP through Security Command Center, enabling organizations to monitor configurations, enforce compliance, and manage risk across their environments.
AWS (Amazon Web Services)
- AWS Security Hub
- AWS Config
- AWS Trusted Advisor (Security Checks)
- Amazon GuardDuty
- AWS IAM Access Analyzer
Microsoft Azure
- Microsoft Defender for Cloud (formerly Azure Security Center).
- Azure Policy
- Azure Security Center (now part of Defender for Cloud)
- Microsoft Entra ID (IAM insights)
GCP (Google Cloud Platform)
- Security Command Center (SCC)
- Cloud Asset Inventory
- Policy Intelligence (IAM Recommender)
- Event Threat Detection
CSPM Benefits
Improved Security Posture
Reduce exposure to misconfigurations and vulnerabilities
Full Visibility
Understand your entire cloud environment
Operational Efficiency
Automate detection and remediation
Compliance Readiness
Align with ISO 27001, SOC 2, and regulatory requirements
Reduced Risk & Cost
Prevent breaches before they happen
The Future of CSPMs
CSPM is evolving from a misconfiguration detection tool into a broader, integrated cloud security capability. It is becoming part of unified platforms like CNAPP, with a stronger focus on identity security, multi-cloud visibility, and continuous risk management across the entire cloud environment.
As cloud adoption grows, CSPM will increasingly leverage AI for risk prioritization and integrate earlier into DevSecOps workflows, enabling organizations to detect and fix issues before deployment. Ultimately, it is shifting from reactive monitoring to proactive, automated security across AWS, Azure, and GCP.
Cloud misconfigurations remain the leading risk in modern environments, and gaining visibility is the first step toward addressing them.
At Reputiva, we help organizations assess and strengthen their cloud security posture across AWS, Azure, and GCP by identifying misconfigurations, tightening identity controls, and aligning with frameworks like ISO 27001.
Start with a Cloud Security Assessment to uncover risks and build a clear remediation roadmap.