Cloud adoption is accelerating, but security isn’t keeping up. The 2026 Cloud Security Report highlights a growing “cloud complexity gap”—a mismatch between the speed of modern cloud environments and the ability of security teams to maintain visibility, detection, and response in real time.
Based on a comprehensive survey of 1,163 senior cybersecurity leaders and practitioners worldwide, the data reveals a widening cloud complexity gap: a structural mismatch between the velocity of modern cloud environments and security teams’ ability to maintain consistent visibility, detection, and response in real time. This gap is not driven by a lack of investment. Budgets are rising, yet maturity lags.
The data suggests the problem is more fundamental, driven by three reinforcing factors:
Fragmented Defenses
As cloud adoption expands, security tooling proliferates alongside it, often without coordination. Disconnected tools, inconsistent controls, and siloed telemetry limit end-to-end visibility and force teams to manually correlate alerts across systems that were never designed to integrate.
Stretched Teams
Persistent talent shortages amplify this fragmentation. Overextended teams rely on alert-driven workflows that slow response and increase the likelihood of missed signals.
Adversaries operating at machine speed
Attackers now use automation and AI to discover misconfigurations, map permission paths, and identify exposed data faster than human-led defenses can respond. As the window between exposure and exploitation compresses, 66% of organizations lack strong confidence in their ability to detect and respond to cloud threats in real time.
The findings increasingly point toward integrated frameworks, interoperable security approaches that consolidate visibility and enable automation grounded in shared context. This approach reduces operational friction and the risk of disruption, data compromise, and regulatory exposure.
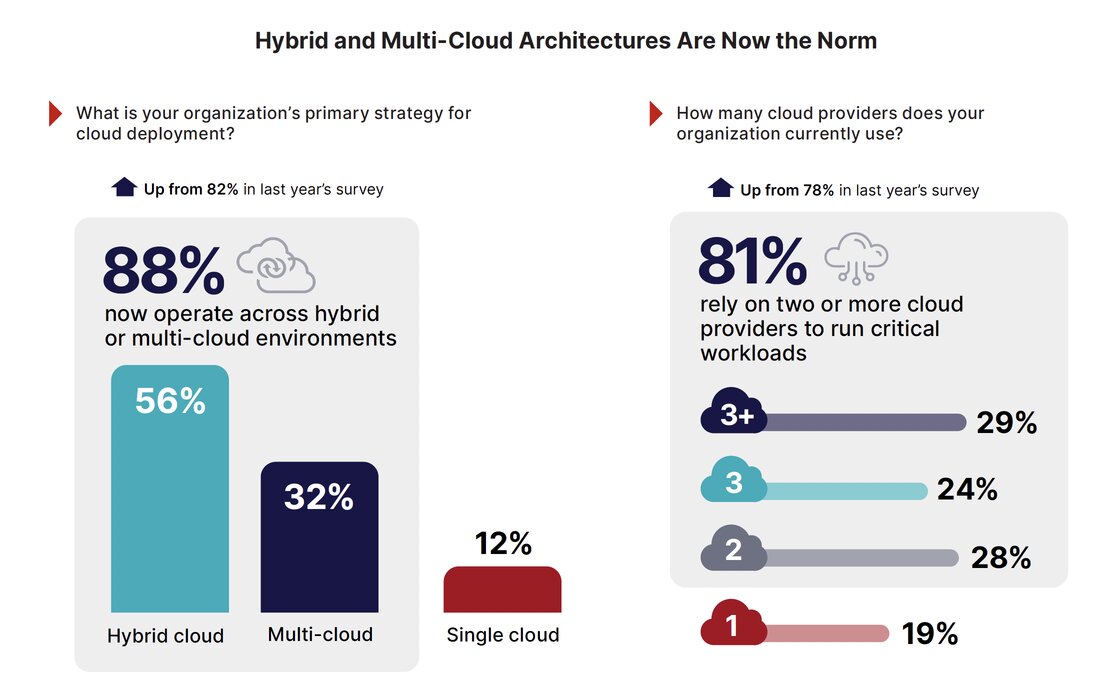
The Multi-Cloud Reality: Complexity is the New Standard
Cloud environments are no longer built around a single provider or a clear boundary. For most organizations, cloud computing now spans multiple public cloud platforms, on-premises infrastructure, Software-as-a-Service (SaaS) applications, and distributed users and devices. This hybrid, multi-cloud model is no longer an intermediate stage: it is the de facto operating model for the enterprise.
As cloud environments grow, the attack surface expands proportionally. Every new provider, service, or identity adds configurations, permissions, and data paths. Assets change constantly, non-human identities multiply, and sensitive data moves across services and regions as part of normal operations. While cloud infrastructure scales automatically, the entire ecosystem becomes increasingly complex to understand.
The Fragmenting Attack Surface
As cloud environments scale, the attack surface does more than expand – it fragments. New cloud accounts, workloads, identities, applications, and data stores are created continuously, often through automated processes and developer-driven workflows. These changes occur across cloud environments that operate independently, leaving security teams to manage exposure that shifts faster than centralized oversight can follow.
Sixty-nine percent of organizations cite tool sprawl and visibility gaps as the top factor limiting cloud security effectiveness. Instead of reducing risk, security teams spend more time navigating multiple consoles and manually correlating alerts across disconnected systems than remediating threats.
The Budget-Maturity Gap
Each new tool adds complexity, including integration work, console management, and additional decision fatigue for already-stretched teams. Returns diminish when the underlying architecture requires manual correlation across systems that lack shared context. As investment grows, much of it is absorbed by the added operational tax of managing disconnected tools rather than by measurable improvements in security outcomes.
This pattern does not imply overinvestment. Instead, it indicates that funding alone cannot close the gap when visibility, coordination, and architectural integration remain constrained.
Complexity Outpaces Talent
The effects of operational complexity are compounded by a persistent shortage of skilled cybersecurity professionals. The survey reveals that 74% of organizations report an active shortage of cybersecurity talent, and 77% express high concern about the industry-wide skills gap. These shortages are especially acute in cloud-specific roles, where expertise must encompass infrastructure, identity, data, and application layers.
Hiring alone cannot close this gap. Even organizations that successfully recruit face lengthy onboarding cycles while cloud environments evolve daily. Manual processes simply cannot scale to keep pace with environments that expand continuously and adversaries operating at machine speed.
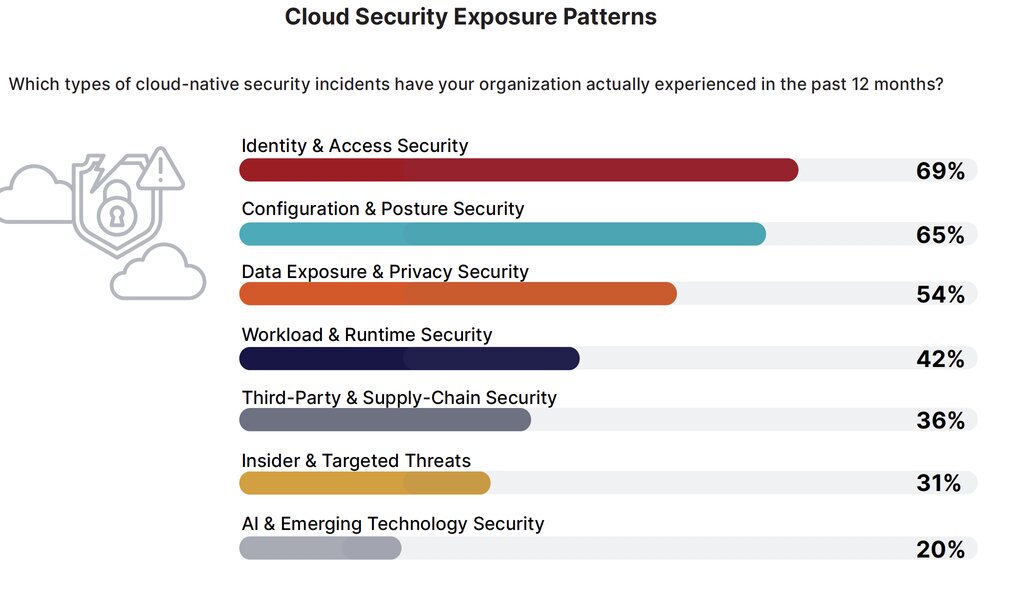
Where Cloud Risk Concentrates
Cloud security risk is concentrated in a small number of recurring areas. Identity and access security ranks as the top cloud-native concern (77%), followed closely by misconfigured cloud services (70%) and data exposure risks (66%). These three areas consistently overshadow other cloud threats, including workload exploits and supply-chain attacks.
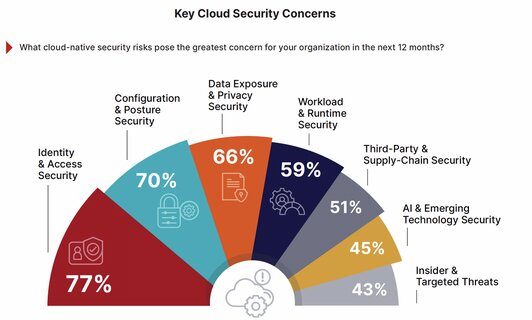
Excessive permissions and stolen credentials create shadow access paths across environments. Misconfigurations unintentionally expose resources and even sensitive data—exposures that are often difficult to inventory and monitor consistently. As cloud estates expand, these risks become more prevalent and systematic rather than incidental
The Risk Exposure Chain
A breach rarely begins and ends with a single vulnerability—attackers follow paths: a misconfiguration exposes a resource, a compromised or overprivileged identity enables access, and sensitive data becomes the target. These stages form an exposure chain of connected risks that point solutions typically only monitor in isolation.
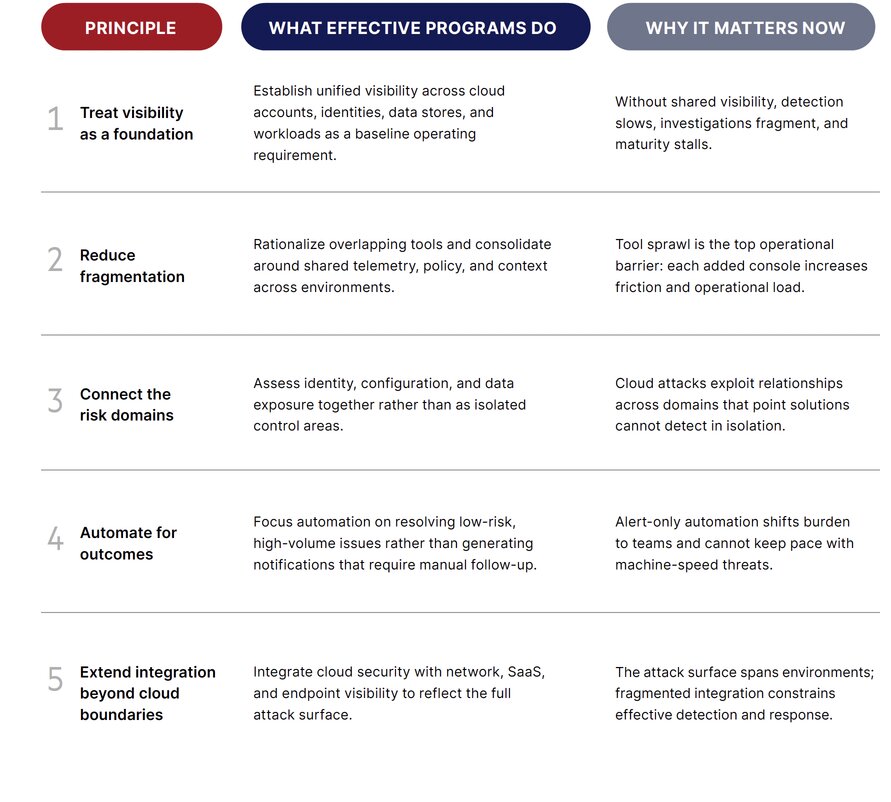
From Insight to Action: Cloud Security Principles
Organizations making progress are not chasing individual tools or isolated capabilities; they are reshaping how cloud security operates day-to-day: the principles below reflect what effective programs consistently prioritize when dealing with scale, fragmentation, and machine-speed threats—practical operating choices grounded in the realities surfaced by the survey.
Close Your Cloud Complexity Gap
Cloud environments are growing, but without the right strategy, so are your risks.
At Reputiva, we help organizations:
- Secure multi-cloud environments across AWS, Azure, and GCP
- Reduce tool sprawl and improve visibility
- Implement identity-first and Zero Trust security
- Align cloud operations with security and governance
Turn Cloud Complexity Into Value. Book an Assessment Today