Cyber threats are evolving faster than ever, and organizations across every industry are under increasing pressure to secure their cloud environments, identities, data, and AI-powered systems.
The 2026 Check Point cybersecurity report highlights how ransomware, phishing, cloud misconfigurations, identity-based attacks, and AI-enabled cyber threats continue to reshape the global threat landscape. The report reinforces a growing reality for modern organizations: cybersecurity is no longer just an IT issue. It is now a business resilience priority.
Cyber Security Trends 2026
As enterprises continue to integrate AI into core business processes, managing how data is shared, processed, and retained by AI systems will remain a critical security challenge in 2026.
In 2026, social engineering activity is expected to intensify further. Generative AI is lowering the barrier to highly convincing attacks, while the rapid adoption of new tools and solutions provides threat actors with an expanding set of trusted workflows to exploit. As a result, social engineering represents a growing, adaptive threat that organizations must treat as a central security challenge.
Smaller groups move faster as RaaS models break down. Extorted victims rose 53% YoY, with 48% growth in new ransomware groups.
Attackers combine email, phone, and user interaction techniques, with email-based attacks accounting for 82% of activity and web-based attacks 18%.
Cyber activity now supports physical and psychological objectives. AI accelerates influence operations and intelligence gathering across civilian infrastructure.
In 2025, cyber operations functioned as an integrated part of warfare along with air power, artillery, and special operations. The impact of cyber operations was realized through sustained interaction with military, political, and informational processes, instead of isolated technical effects.
AI as a force multiplier
Attackers are integrating AI, identity abuse, exposure exploitation, and ransomware into their campaigns. Data indicates that attackers are linking access, execution, and impact across various domains, from AI-driven social engineering and automation to the transformation of ransomware into a data-driven extortion economy. Edge devices and exposed infrastructure are increasingly used as launch points. The report views AI as a force multiplier that enhances targeting, scale, and adaptation in attacker activities, while also influencing risk prioritization and operational responses.
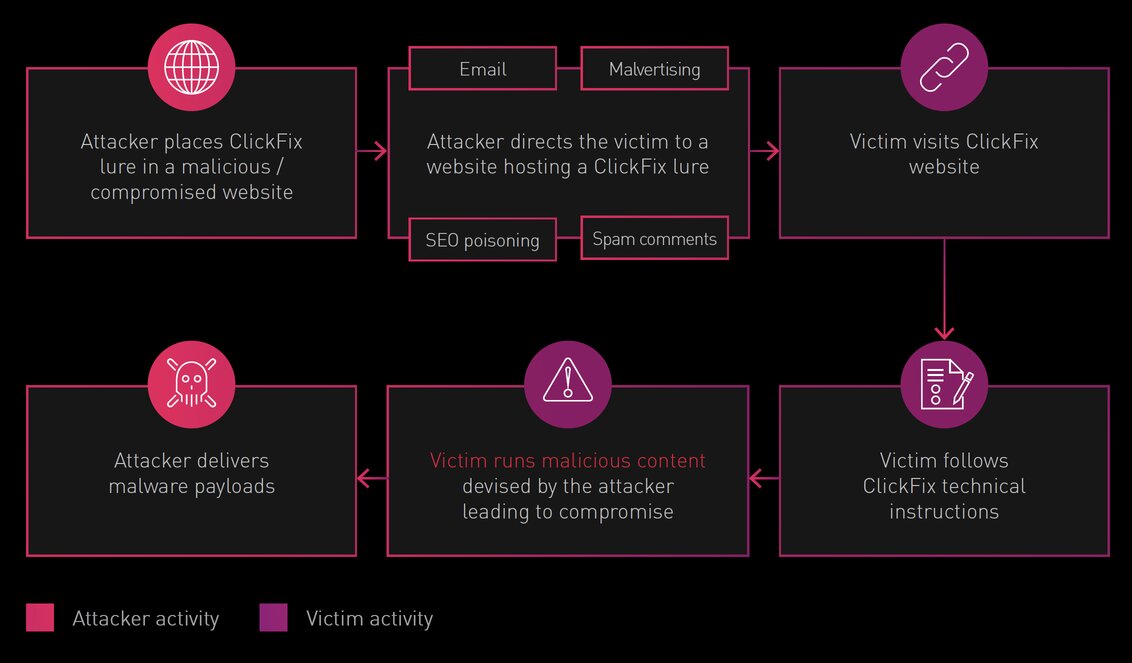
ClickFix: Social Engineering That Shifts Execution to the User
First observed in 2024, ClickFix is an initial access method in which attackers manipulate users into executing malicious actions by presenting them with fraudulent instructions. These instructions, typically delivered through compromised or attacker-controlled websites, malvertising, or brand-impersonation emails, are crafted to resemble routine verification steps such as CAPTCHAs, validation checks, or error fixes.
By appearing as legitimate steps required to continue normal activity, users are manipulated into running attacker-controlled content that ultimately delivers malware.
ConsentFix
In parallel, attackers have extended ClickFix’s approach past code execution to account compromise. ConsentFix, which emerged toward the end of 2025, applies similar social engineering principles to cloud environments.
ConsentFix tricks users into completing a legitimate Microsoft/Azure OAuth login flow. It then instructs them to copy and paste a localhost URL that contains an OAuth authorization code into an attacker-controlled page. The stolen code is used to obtain tokens and gain access to the user’s Microsoft account without capturing a password and completing multi-factor authentication (MFA).
Coercing victims to initiate malicious activity on their own systems reflects a broader shift in attackers’ social engineering strategies, which abuse user trust in legitimate processes across endpoints, browsers, and cloud identity platforms.
Voice-Based Social Engineering – The Weapon of Choice for Major Attacks
Voice phishing and impersonation gained significant traction in 2025, proving to be a highly effective means to exploit user trust. In these attacks, threat actors pose as trusted or authoritative figures and, following targeted reconnaissance, use rehearsed scripts to pressure victims to take actions such as resetting credentials, changing MFA codes, or granting network access.
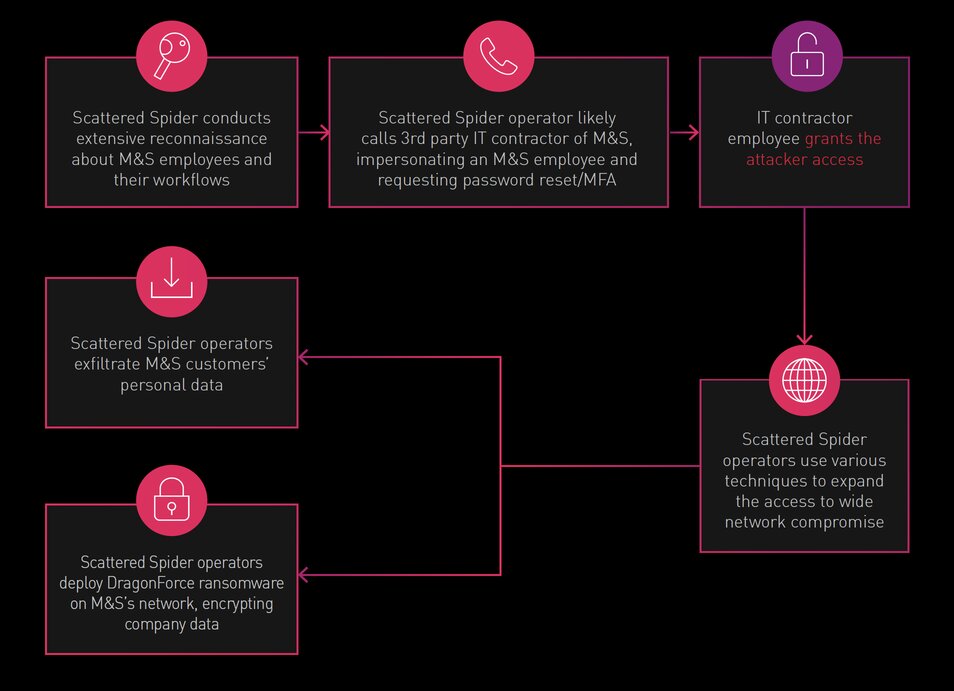
In 2025, voice-based impersonation became a preferred technique among highly sophisticated threat groups targeting major brands. These actors conducted in-depth reconnaissance, leveraged multiple communication platforms to engage victims, and executed complex, multistage social engineering scripts to achieve their goals. In several cases, voice-driven campaigns enabled attackers to gain initial access for some of the year’s most damaging high-impact enterprise intrusions.
According to FBI reporting, the voice-enabled fraud and account takeover incidents in 2025 resulted in losses exceeding $250 million.
AI LANDSCAPE: FROM INTEGRATION TO AUTONOMY
In 2025, Artificial intelligence (AI) was so deeply embedded in cyber activity that distinguishing “AI-related attacks” from general digital operations became increasingly challenging. In contrast to 2023–2024, when attackers’ use of AI was easily recognizable, in 2025 AI use became so commonplace that it faded into the background of attack operations.
AI now underpins software development, social engineering malware design, data mining, influence operations, reconnaissance, vulnerability discovery, and even post-exploitation activity.
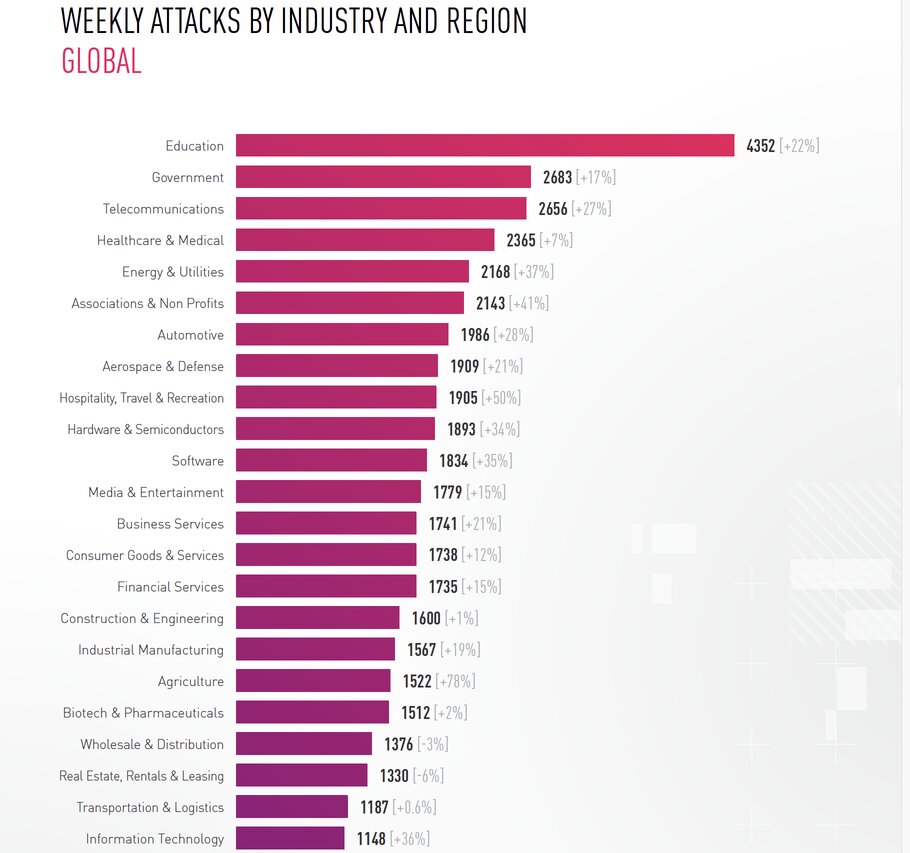
Most targeted industry: Education
In 2025, cyber attack activity increased across all regions and nearly every industry. Once again, Education remained the most targeted sector, averaging 4,352 attacks per organization per week, a 22% increase over the previous year. Government, Telecommunications, and Healthcare & Medical also reached their highest observed weekly attack volumes.
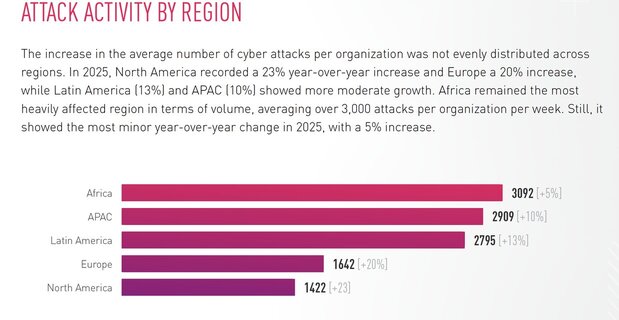
Most attacked continent: Africa
The increase in the average number of cyber attacks per organization was not evenly distributed across regions. In 2025, North America recorded a 23% year-over-year increase and Europe a 20% increase, while Latin America (13%) and APAC (10%) showed more moderate growth. Africa remained the most heavily affected region in terms of volume, averaging over 3,000 attacks per organization per week. Still, it showed the most minor year-over-year change in 2025, with a 5% increase.
2026 INDUSTRY PREDICTIONS: THE FUTURE OF CYBER SECURITY
Agentic AI Transitions from Assistance to Operational Autonomy
2026 will see agentic AI move to the mainstream. Autonomous systems capable of reasoning, planning, and acting with minimal human input move us from assistants who draft content to agents who execute strategy. These systems will allocate budgets, monitor production lines, and reroute logistics, all in real-time.
Prompt Injection and Data Poisoning – AI Models Become the New Zero-Day
As generative AI is embedded across customer facing services, internal workflows, and security operations, AI models themselves are emerging as high-value attack surfaces. In 2026, adversaries will increasingly exploit prompt injection, embedding covert instructions in text, code, or documents that manipulate model behavior, as well as data poisoning, where tainted inputs distort or compromise training data.
In 2026, AI security leaders will differentiate themselves by operationalizing governance, validation, and continuous oversight to ensure AI systems remain trustworthy at scale.
Supply Chain and SaaS Exposure Intensifies Across Hyperconnected Ecosystems
Enterprises now operate within webs of vendors, APIs, and integrations, creating attack paths where just one weak supplier can lead to widespread compromise. As ecosystems grow more automated and interdependent, incidents spread faster through shared code, tokens, and cloud services than they can be traced.
Trust Is the New Perimeter: Deepfakes and Conversational Fraud
Generative AI has blurred the line between genuine and fabricated content. Voice cloning, real-time synthetic video, and AI-driven chat interactions now enable attackers to bypass traditional identity and access controls, including multi-factor authentication.
Quantum Risk Moves From Long- Term Concern to Near-Term Action
Quantum computing may still be years from cracking today’s encryption, but the threat has already changed, and should continue to change, enterprise behavior. Governments, cloud providers, and large enterprises are racing to secure cryptographic agility, migrating from vulnerable Rivest–Shamir–Adleman (RSA) and Elliptic Curve Cryptography (ECC) algorithms to post-quantum cryptography (PQC) standards before adversaries can weaponize them.
Quantum risk is not about tomorrow’s machines. It is about today’s data. Every organization must assume its encrypted assets are already being harvested and prepare for a world where prevention depends on cryptographic agility.
AI Becomes a Strategic Decision Engine
AI is steadily changing the foundations of cybersecurity. What once served mainly as a tool for operational efficiency is now influencing how both attackers and defenders plan, adapt, and execute their strategies. The industry is moving into a phase where AI is no longer a supporting capability, but an embedded element in detection, analysis, and decision-making workflows.
The AI Reality Check
After two years of near-frantic AI adoption, we will experience our first major recalibration. Many organizations that rushed to integrate generative AI tools will discover ungoverned systems, exposed APIs, and compliance blind spots. Shadow AI, employee-initiated tools using corporate data, will proliferate, creating invisible data leaks and inconsistent security standards.
AI’s first disruption was speed; its second will be governance. 2026 will reward those who treat AI not as a shortcut but as a capability to be secured, audited, and improved.
Regulation and Accountability Expand – Cyber Resilience Becomes a License to Operate
Regulators worldwide are closing the gap between innovation and accountability. In 2026, regulation ceases to be a reactive approach. Frameworks such as the EU’s NIS2 Directive, the EU AI Act, and the U.S. SEC incident-disclosure rules will converge on a single principle: cyber security must be measurable and demonstrable in real-time. Governments will now expect continuous proof of resilience. Organizations are expected to demonstrate that their preventive controls, incident response plans, and data protection measures are consistently enforced.
This shift will mark the end of the era of “annual compliance.” Enterprises will rely on automated compliance monitoring, machine-readable policies, real-time attestations, and AI-based risk analytics. Boards and CEOs will carry personal responsibility for oversight.
From Reactive Security to Cyber Resilience
The Check Point Cybersecurity Report 2026 reinforces what many organizations are already experiencing: cyber threats are becoming more identity-driven, AI-enabled, and cloud-focused.
As businesses continue adopting AWS, Azure, and GCP services, the attack surface expands beyond traditional networks into cloud workloads, SaaS platforms, APIs, identities, and AI-powered tools. Unfortunately, many organizations are still operating with fragmented visibility, inconsistent security controls, and limited cloud security expertise.
At Reputiva, we believe modern cybersecurity requires a proactive and continuous approach built around:
- Cloud Security & Misconfiguration Management
- Identity & Access Governance
- Zero Trust Security Principles
- Security Awareness & Training
- Continuous Monitoring & Threat Visibility
- AI & Data Security Readiness
Organizations that invest early in security maturity, cloud governance, and employee awareness will be far better positioned to reduce risk, improve resilience, and adapt to the evolving threat landscape.
Looking to strengthen your organization’s cybersecurity posture?
At Reputiva, we help organizations move beyond reactive security by strengthening cloud security, identity governance, Zero Trust strategies, and cybersecurity awareness across AWS, Azure, and GCP environments.
As organizations continue accelerating cloud and AI adoption, security can no longer be treated as a one-time project. It must become part of how organizations operate, scale, and innovate securely.
Book a Cloud Strategy & Security Assessment with Reputiva today and start building a more resilient cybersecurity foundation.


