The latest insights from Google Cloud Security and its Mandiant team in the M-Trends 2026 Report: Real-World Investigations and Actionable Defense Insights provide a frontline view into how modern attacks actually unfold. The report provides an outlook on the threats and tactics used in breaches, grounded in Mandiant’s 2025 investigations of over 500k hours of incidents.
The findings highlight a critical shift: attackers are operating faster, more coordinated, and more efficient than ever, making visibility, identity security, and proactive defense essential.
We don’t consider 2025 to be the year where breaches were the direct result of AI. From our view on the frontlines, the vast majority of successful intrusions still stem from human and systemic failures.
M-Trends is a definitive look at the threats and tactics used in breaches, grounded in over 500k hours of frontline incident investigations conducted by Mandiant in 2025. Conducted by Mandiant and the Google Threat Intelligence Group (GTIG), the report is a comprehensive view of the modern threat landscape and emerging threats that may drive future attacks.
Top M-Trends Observations
Hand-off Trend
One threat actor gains initial access and then provides access to a separate actor that typically conducts higher-impact operations, such as ransomware. This hand-off is happening so quickly (sometimes under 30 seconds) that it creates a scenario in which alerts traditionally considered “lower priority” can quickly become significant compromises.
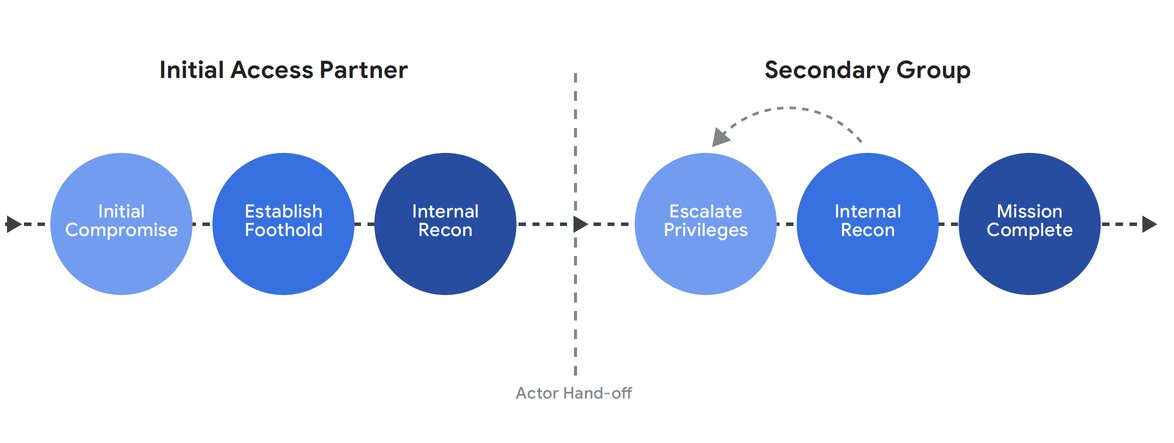
In 2025, 9% of the incidents Mandiant investigated followed a “division of labor” model for the initial intrusion, up from 4% in 2022. This model involves two or more threat groups, where one group focuses exclusively on initial access operations to gain a foothold in an environment, and the subsequent group or groups perform the remaining stages of the attack lifecycle.
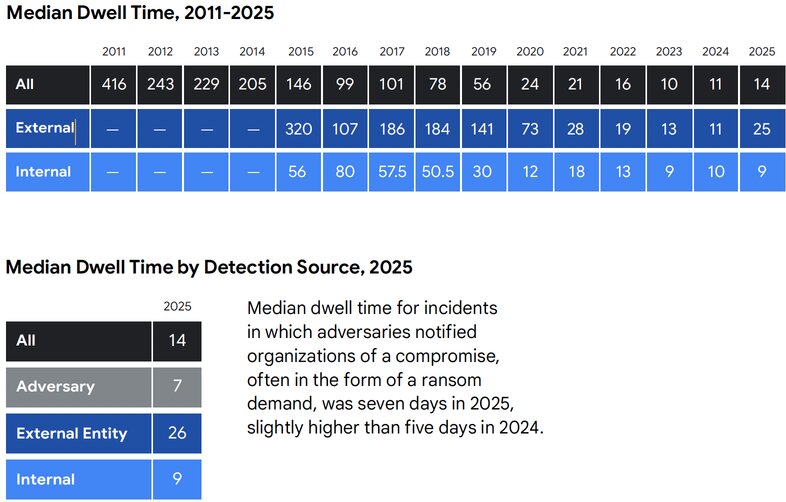
Dwell Time rise
Global median dwell time has risen to 14 days from 11 days, driven largely by long-term espionage and DPRK IT worker operations. The longer adversaries remain undetected, the greater the cost and complexity of remediation.
Traditional Endpoint is not sufficient
Financially motivated and cyber espionage groups continue to abuse native functionalities in on-premises and cloud environments, as well as legitimate tools, to reduce opportunities for detection. This means traditional endpoint security relying on malware signatures is not sufficient.
Ransomware Shift: Data Theft to Recovery Denial
Ransomware operators have shifted their primary objective from data theft to the deliberate denial of recovery, systematically targeting backup infrastructure, identity services, and virtualization management planes. By rendering recovery impossible, threat actors put immense pressure on organizations to pay ransom demands.
Organizations should prioritize the security of infrastructure such as backups, identity services, and the virtualization layer, which attackers are now systematically targeting to deny recovery. Hardening edge and core network devices remains critical, especially since exploits continue to be the most common entry point for adversaries.
Initial Infection Vector
For the sixth year running, exploits represented the most frequently observed initial infection vector in 2025 Mandiant incident response investigations. Exploits comprised 32% of investigations in which an initial infection vector could be identified.
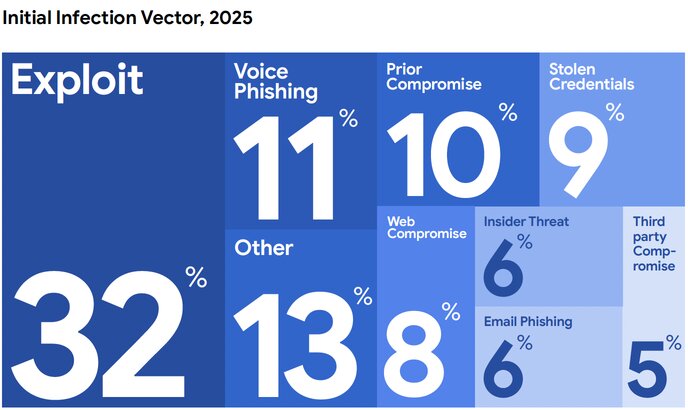
The proportion of incidents stemming from social engineering through voice phishing and messaging apps noticeably increased in 2025 compared to prior years, with voice phishing emerging as the second-most commonly observed vector in 2025 investigations at 11%.
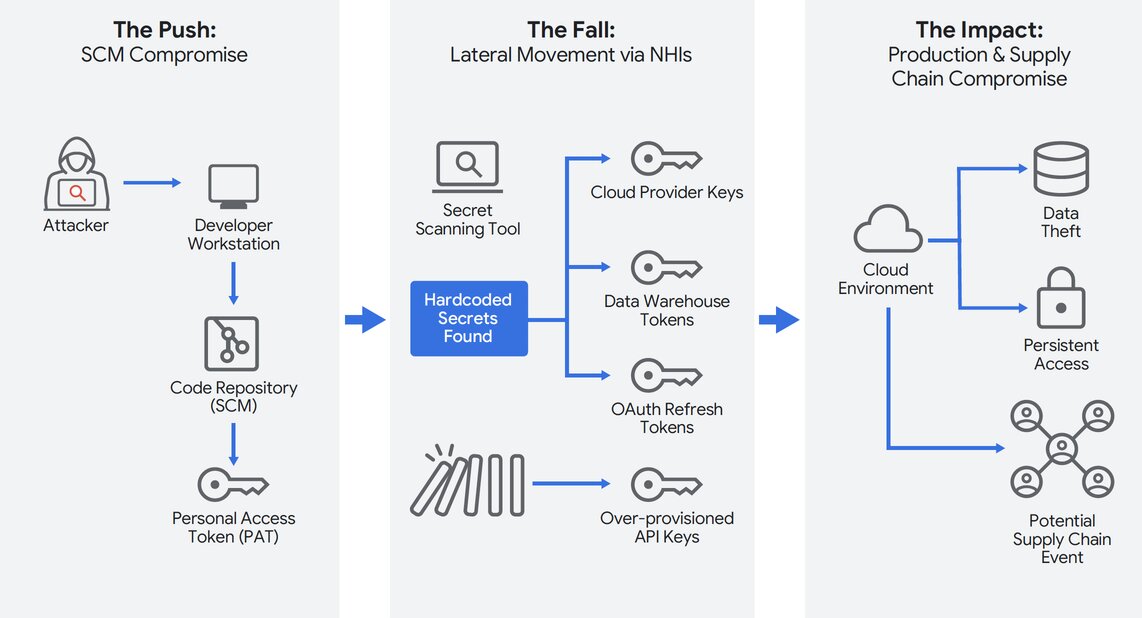
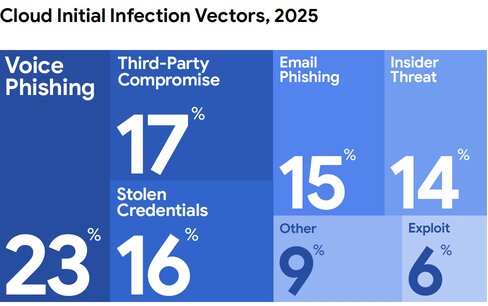
Cloud Compromise
In 2025, the most common initial infection vector found during Mandiant investigations of cloud-related compromises was voice phishing, at 23%, followed by third-party compromise (17%), stolen credentials (16%), email phishing (15%), insider threat (14%), and exploits (6%). Mandiant identified evidence of data theft in 59% of cloud compromises. Just over a third of cases, 34%, supported financially motivated objectives, including employment fraud, data theft extortion, ransomware, payment redirection fraud, and theft.
In 2025, threat clusters have increasingly adopted AI tools to achieve productivity gains in different stages of the attack lifecycle, particularly in tasks such as reconnaissance, social engineering, and malware development. In 2025, Mandiant investigations identified threat clusters using AI-themed lures, stealing credentials for AI applications, and targeting companies developing AI technologies.
Conclusion
Adversaries are leveraging AI to accelerate attacks, shifting from mass, static email campaigns toward hyper-personalized, voice-based social engineering, and deploying malware capable of querying large language models mid-execution. Yet, despite these rapid technological advancements, the incidents investigated by Mandiant for M-Trends 2026 primarily stemmed from fundamental human and systemic failures.
Organizations must aggressively manage internet-facing attack surfaces, strictly isolate external-facing web application servers, and pivot security awareness training beyond the inbox to address live, interactive social engineering.
What This Means for Your Organization
The findings from the M-Trends 2026 Report are clear: most successful breaches are not driven solely by advanced zero-day exploits, but by speed, identity gaps, and a lack of visibility across environments.
1. Prevention Alone Is Not Enough
- Exploits remain the #1 initial access vector (32%)
- Attackers are finding ways in consistently
What this means:
- You must assume breach is inevitable
- Focus shifts to: Detection, Response and Containment
2. Attackers Move Faster Than Your Alerts
- Attack “hand-offs” can happen in under 30 seconds
What this means:
- “Low priority alerts” are dangerous
- Security teams need: Real-time monitoring and Automated response
3. Identity Is the New Attack Surface
- Credential abuse, phishing, and access misuse are dominant patterns
- Voice phishing is now a top attack vector
What this means:
- Traditional perimeter security is obsolete
- You must prioritize: IAM hardening, MFA enforcement and Least privilege
4. Visibility Gaps Are Your Biggest Weakness
- 52% of organizations detect breaches internally, but many still rely on external alerts
- Dwell time increased to 14 days globally
What this means:
- Attackers are staying longer undetected
- You need: Centralized visibility and Continuous monitoring
5. Ransomware Is Now a Resilience Problem
- Attackers target: Backups, Identity systems and Virtualization layers
What this means:
- It’s no longer just about prevention
- It’s about: Recovery capability and Business continuity
Cloud Complexity Is Increasing Risk
- Attackers abuse: Native tools and Legitimate cloud functionality
What this means:
- Misconfigurations and weak governance = entry points
- You need: CSPM, Cloud visibility and Policy enforcement
Modern cyberattacks are not just more sophisticated; they are faster, more coordinated, and designed to exploit gaps in visibility and identity.
At Reputiva, we help organizations strengthen their security posture across AWS, Azure, and GCP by combining cloud security architecture, identity-first security, and real-world threat insights to reduce risk and improve resilience.
Start with a Cloud Security Assessment to identify vulnerabilities, improve visibility, and build a proactive defense strategy aligned with today’s threat landscape.